Why WebAssembly is the future of web development?
In 2025, the expectations for web applications are higher than ever: speed, interactivity, and the ability to handle complex tasks directly in the browser. That’s where WebAssembly (or Wasm) comes in, a technology that allows you to run high-performance code in a safe and portable way. Unlike JavaScript, which is interpreted, WebAssembly runs compiled code from languages like C, C++, or Rust, bringing web performance close to that of native applications.
If you are a developer who wants to stand out, learning WebAssembly today is an investment for the future. In this article I will explain what it is, how it works and I will guide you step by step in a practical example to integrate it into a web project. Ready to make your applications lightning fast? Let’s get started!
What is WebAssembly and how does it work?
WebAssembly is a binary format that acts as a “virtual machine” for the web. It allows you to compile code written in high-performance languages (Rust, C++, Go, etc.) into a format that can be run by major modern browsers such as Chrome, Firefox, and Safari.
The main advantages of WebAssembly
- Speed: Thanks to preemptive compilation, Wasm is much faster than JavaScript for intensive calculations.
- Portability: Works on any platform that supports a modern browser.
- Security: Runs code in a sandbox environment, providing protection against exploits.
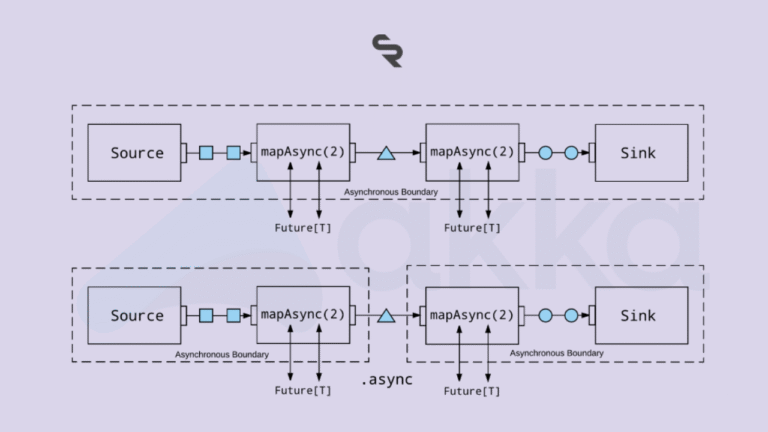
But how does it integrate with the web? Simple: WebAssembly works hand in hand with JavaScript, allowing you to use Wasm for the performance-critical parts and JS for the general logic.
Hands-on Tutorial: Creating a Function with WebAssembly and Rust
To really understand WebAssembly, let’s get to work with a concrete example. We’ll create a simple function in Rust that adds two numbers, compile it into WebAssembly, and embed it in an HTML page.
Prerequisites
- Install Rust: Visit this guide at the link and follow the instructions.
- Install wasm-pack : Run cargo install wasm-pack in terminal.
- A code editor (e.g. VS Code) and Node.js for the local server.
Step 1 – Set up your project
- Create a new directory: mkdir wasm-demo && cd wasm-demo .
- Initialize a Rust project: cargo new –lib wasm-lib && cd wasm-lib .
- Update the Cargo.toml file to add WebAssembly support:
[package]
name = "wasm-lib"
version = "0.1.0"
edition = "2021"
[lib]
crate-type = ["cdylib"]
[dependencies]
wasm-bindgen = "0.2"Step 2 – Write the Rust code
Edit src/lib.rs with this function:
use wasm_bindgen::prelude::*;
#[wasm_bindgen]
pub fn add(a: i32, b: i32) -> i32 {
a + b
}This code defines a function add that adds two integers and makes it accessible to JavaScript via wasm_bindgen .
Step 3 – Compile in WebAssembly
Run in terminal:
wasm-pack build --target webThis generates WebAssembly files in the pkg directory .
Step 4 – Embed into HTML
Create an index.html file in the root of your project:
<!DOCTYPE html>
<html lang="it">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>WebAssembly Demo 2025</title>
</head>
<body>
<h1>Calcolatrice WebAssembly</h1>
<p>Risultato: <span id="result"></span></p>
<script type="module">
import init, { add } from './wasm-lib/pkg/wasm_lib.js';
async function run() {
await init();
const result = add(5, 3);
document.getElementById('result').innerText = result;
}
run();
</script>
</body>
</html>Result: Step 5 – Test the result
Start a local server (e.g. with npx serve ) and open your browser. You will see ” Result: 8 “. You have just used WebAssembly to perform a computation!
Real-world WebAssembly Applications in 2025
WebAssembly is not just a theoretical exercise. Here are some real-world use cases:
- Browser Games : Platforms like Unity are using Wasm to bring complex 3D games to the web.
- Multimedia editing : Adobe has integrated WebAssembly into tools like Photoshop for the web.
- Machine Learning : Frameworks like TensorFlow.js leverage Wasm to accelerate ML computations in the browser.
By 2025, with increasingly powerful browsers, expect Wasm will become a standard for next-generation web applications.
Advantages and limitations of WebAssembly
Pro
- Near-native performance for intensive computations.
- Compatibility with languages other than JavaScript.
- Ease of integration with existing code.
Against
- Learning curve for those new to compiled languages.
- Wasm file size larger than JS for small scripts.
- Debugging is even less intuitive than JavaScript.
Why learn WebAssembly today?
WebAssembly is a technology that is shaping the future of the web, and in 2025 it will be a valuable skill for developers. With this tutorial you have seen how simple it is to get started, but the possibilities are endless: from games to data analysis tools, Wasm opens new doors.